
Fake Huorong security site infects users with ValleyRAT
One extra letter in the domain is all it takes to hand over remote control of your system.
Data analysis, big data, and business intelligence

One extra letter in the domain is all it takes to hand over remote control of your system.
Researchers investigated the zero-knowledge claims of password managers—and found some possible attack scenarios.
OpenClaw is a hot topic at the moment. But what is it and how can you use the 24/7 AI assistant in a safe way?
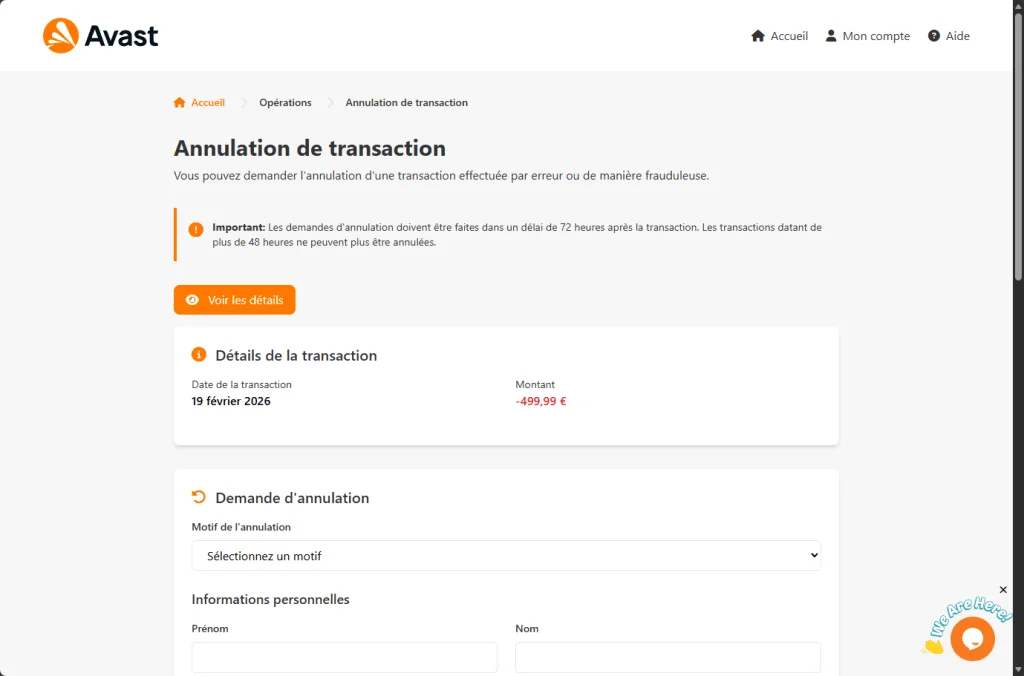
A convincing fake Avast site displays a €499.99 charge and promises a refund. Instead, it harvests your name, address, and full credit card details.
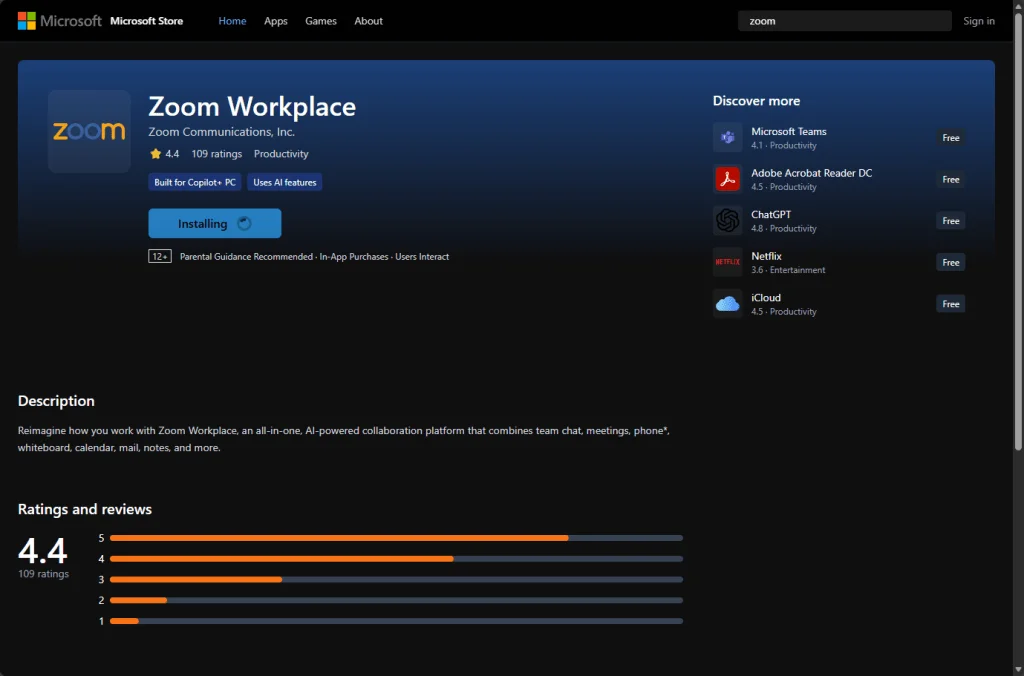
A fake Zoom meeting page looks real, triggers a bogus “update,” and silently installs a legitimate commercial monitoring product.
Los Angeles County sued the online gaming platform Roblox for its alleged failure to protect children from danger.
Ofcom and the Information Commissioner's Office respectively fined a US porn company and Reddit for failing to protect children online.
Unsealed court records reveal Instagram executives discussed explicit messages to teens years before a blur feature was introduced.
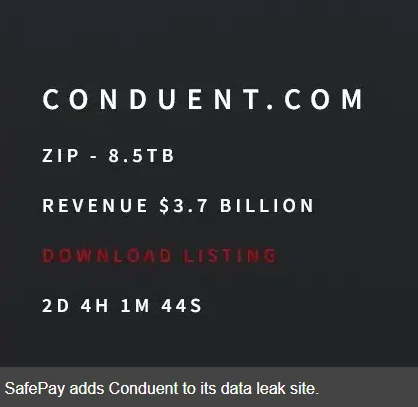
A third-party breach at Conduent now affects 25 million Americans—many never knew their data flowed through its systems.
APT stands for Advanced Persistent Threat. But what does that actually mean, and how does it translate into the kind of threat you’re facing?
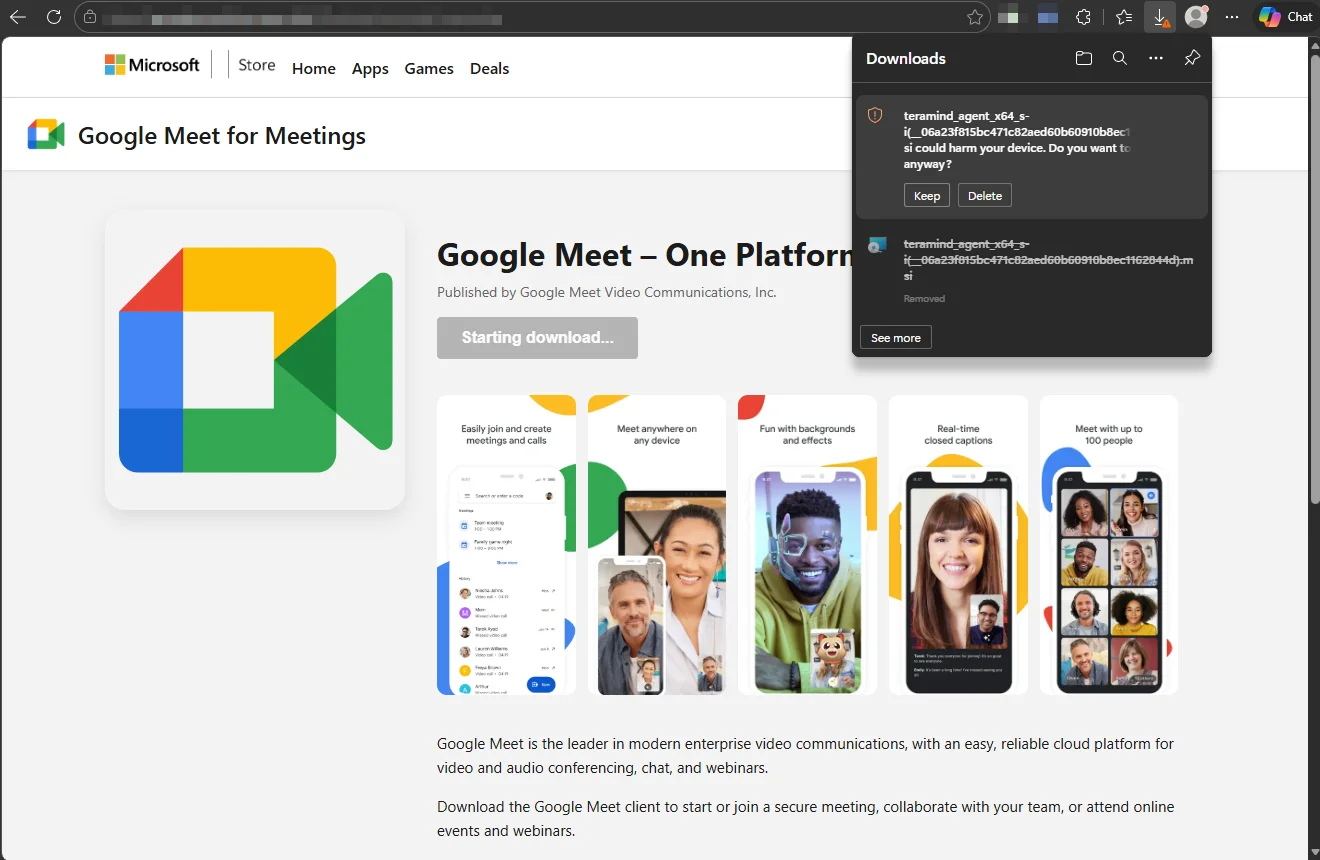
Attackers don’t always need custom malware. Sometimes they just need a trusted brand and a legitimate tool.
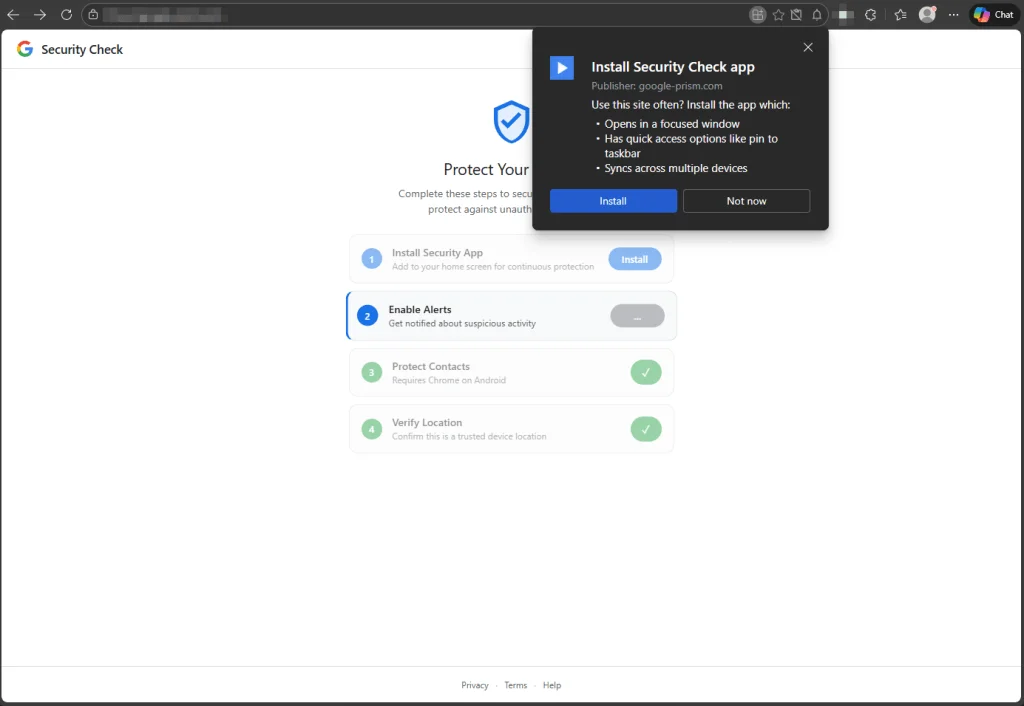
Disguised as a security check, this fake Google alert uses browser permissions to harvest contacts, location data, and more.
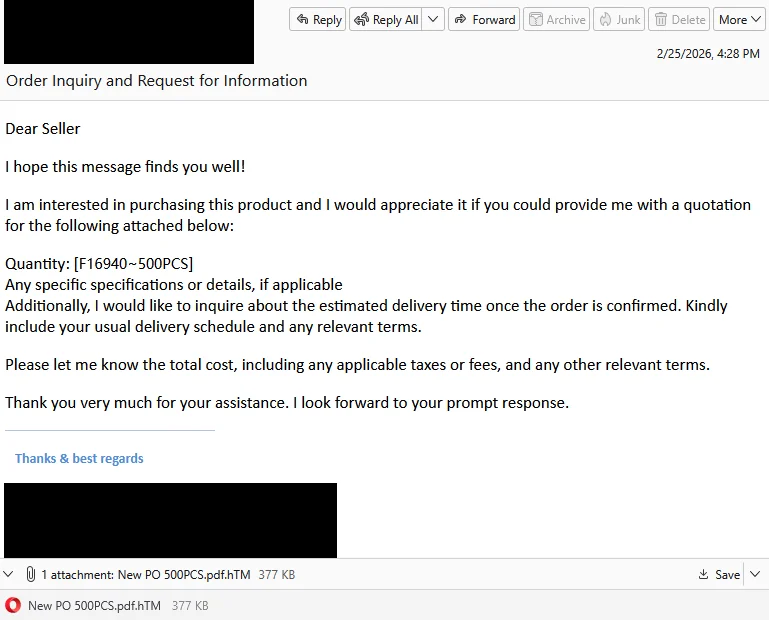
A fake purchase order attachment turned out to be a phishing page designed to harvest your login details.
As Samsung settles a lawsuit over how its smart TVs collect and monetize viewing data using ACR, here's how the rest of us can limit the data we're sharing.